MSRC Blog:
Released: Apr 9, 2024
Last updated: Apr 11, 2024
Assigning CNA: Intel Corporation
CVE-2022-0001
Impact: Information Disclosure Max Severity: Important
Weakness: CWE-1303: Non-Transparent Sharing of Microarchitectural Resources
CVSS Source: Intel Corporation
CVSS: 3.1 4.7 / 4.1
Executive Summary
This CVE was assigned by Intel. Please see CVE-2022-0001 on CVE.org for more information.Exploitability
The following table provides an exploitability assessment for this vulnerability at the time of original publication.| Publicly disclosed | Exploited | Exploitability assessment |
|---|---|---|
| No | No | Exploitation Less Likely |
FAQ
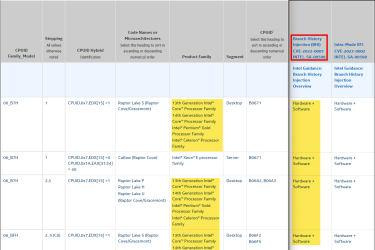
Why is this Intel CVE included in the Security Update Guide?The vulnerability assigned to this CVE is in certain processor models offered by Intel and was initially disclosed March 8, 2022. Intel published updates April 9, 2024 and this CVE is being documented in the Security Update Guide to inform customers of the available mitigation and its potential performance impact. The mitigation for this vulnerability is disabled by default and manual action is required for customers to be protected.
The following documentation was updated by Intel on April 9, 2024 and can be referenced for more information:
- CVE-2022-0001
- Branch History Injection and Intra-mode Branch Target Injection
- Branch History Injection and Intra-mode Branch Target Injection
We are providing the following registry information to enable the mitigations for this CVE.
Important: This section, method, or task contains steps that tell you how to modify the registry. However, serious problems might occur if you modify the registry incorrectly. Therefore, make sure that you follow these steps carefully. For added protection, back up the registry before you modify it. Then, you can restore the registry if a problem occurs. For more information about how to back up and restore the registry see How to back up and restore the registry in Windows.
To enable the mitigation for CVE-2022-0001 on Windows devices and clients using Intel Processors:
-
Code:
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverride /t REG_DWORD /d 0x00800000 /f -
Code:
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management" /v FeatureSettingsOverrideMask /t REG_DWORD /d 0x00000003 /f
Add: Download
Undo: Download
Customers who wish to implement the mitigation within their systems can also refer to the following for more information.
- Windows Server and Azure Stack HCI customers: See Microsoft Knowledge Base Article 4072698
- Windows client guidance for IT Pros: See Microsoft Knowledge Base Article 4073119
- Windows Device customers: See Microsoft Knowledge Base Article 4073757
- Specify spectre_bhi=on on the kernel command line. For more information about kernel command-line parameters see The kernel’s command-line parameters — The Linux Kernel documentation
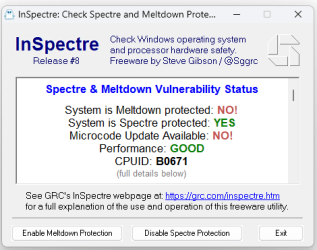
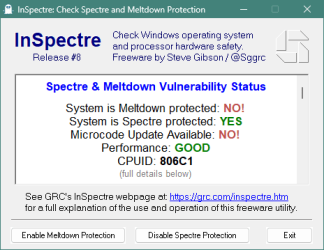
In some cases, installing these updates will have a performance impact. In testing Microsoft has seen some performance impact with this mitigation. Microsoft values the security of its software and services but made the decision to allow users and administrators to evaluate the performance impact and risk exposure before deciding to enable the mitigation.
Read more:
Security Update Guide - Microsoft Security Response Center
Attachments
Last edited: